VPN Protocols: Comparison and How to Choose the Right One
Not too long ago we were looking to install the best antiviruses to keep our devices safe. But with the increasingly upgraded security protocols in our computers and laptops, VPNs are becoming the new security measure for most of us.
Today, many different VPN service providers can help keep your online activities safe and enable you to access geo-restricted content worldwide. And at the heart of the underlying technology of virtual private networks are VPN protocols.
This guide will break down everything there is to know about VPN protocols. We'll explain what part they play in your security, connection speeds, and compatibility, and compare the main features of the most popular protocols to help you choose the best VPN protocol for you.

Adomas Šulcas
9 min read

What Are VPN Protocols?
To define a VPN protocol, we should first lay out a brief outline of a VPN. A Virtual Private Network (VPN) provides a masked and secure connection to the internet. When you connect to a VPN service, your IP address is made anonymous, or masked by an IP address from a different location.
A VPN protocol is a set of specific rules and processes that determine how data is transmitted over a specific VPN. Basically, a VPN protocol technology creates a secure tunnel with your device (or devices) on one end and the internet on the other. It essentially makes sure that all your activity online is safe from any prying eyes or other unsavory characters on the web.
As there are many VPN service providers, each of them employs different VPN protocols that deliver speed, security, and compatibility. However, some protocols emphasize one or two elements in particular, like speed and security. Examples of the most popular VPN protocols include:
- OpenVPN.
- WireGuard.
- Internet Key Exchange version 2 / Internet Protocol Security (IKEv2/IPsec).
- Layer 2 Tunneling Protocol / Internet Protocol Security (L2TP/IPsec).
- Point-to-Point Tunneling Protocol (PPTP).
- Secure Socket Tunneling Protocol (SSTP).
A Quick Comparison Table of VPN Protocols
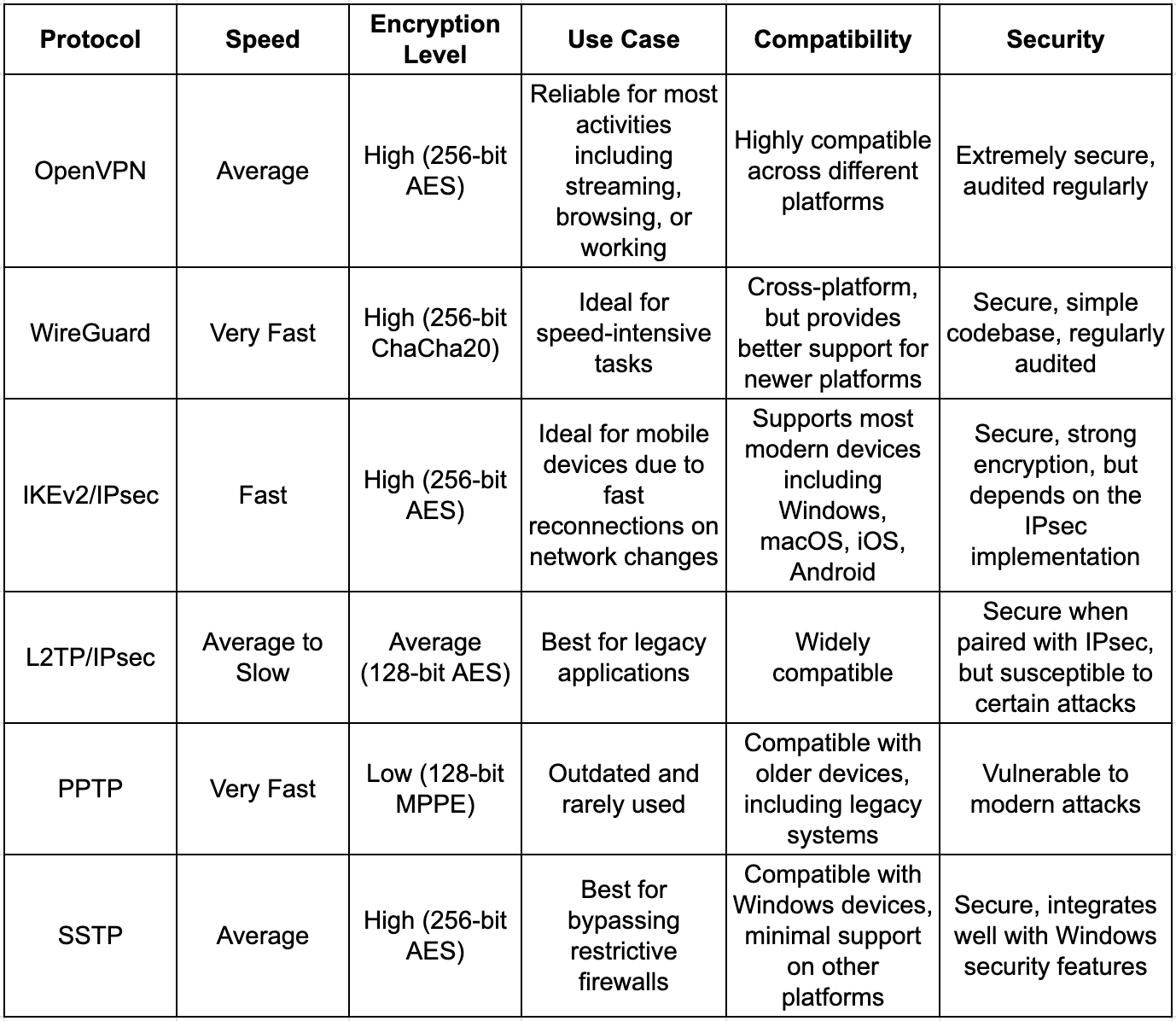
Overview of the Most Popular VPN Protocols
OpenVPN
The OpenVPN protocol was launched in 2001 and to this day, it remains one of the most widely used VPN protocols. OpenVPN is an open-source technology that allows developers and security experts to work together on continuously improving its code.
Thanks to years of development from different specialists and experts, OpenVPN is capable of delivering a fast service for hassle-free streaming or gaming, and high-level security for protected online activity. It's one of the best VPN protocols that's used by ExpressVPN, CometVPN, NordVPN, and CyberGhost, available on multiple devices and operating systems.
WireGuard
Among the most common VPN protocols, WireGuard stands out as a next-generation protocol. It was introduced in 2015 and is built to be lightweight and efficient, with a simple and well-audited codebase to minimize vulnerability risks. If you're looking for the fastest VPN protocol, WireGuard is the one to choose.
WireGuard uses top-tier cryptographic and encryption protocols like ChaCha20 which is known for delivering amazing speeds and security. Additionally, compared to other VPN protocols, WireGuard offers faster connection speeds and lower latency, making it ideal for intense activities requiring a strong stable connection, like streaming or gaming.
Most VPN service providers use a combination of VPN protocols, that's why in addition to utilizing the OpenVPN protocol, NordVPN and CometVPN also use WireGuard. Other services include Surfshark and Mullvad.
IKEv2/IPsec
Internet Key Exchange version 2 (IKEv2) was launched in 2005 while Internet Protocol Security (IPsec) was introduced way back in the 1990s. IKEv2 and IPsec are known for high-level security, speed, and stability. These VPN protocols are especially great for mobile devices, allowing quick reconnections when switching between networks or going from Wi-Fi to mobile data without disturbing your online connection.
As with all other VPN protocols, IKEv2 and IPsec utilize strong encryption protocols to enhance security. Many well-known VPN service providers like ExpressVPN, ProtonVPN, and CyberGhost, include IKEv2 and IPsec as an available option for their mobile users.
L2TP/IPsec
When you look back at the history of VPN protocols, Layer 2 Tunneling Protocol (L2TP) was developed in the 1990s and is used today in combination with IPsec. While outdated, L2TP/IPSec remains a trusted and reliable protocol.
The technology behind L2TP works by creating a data transmission tunnel while IPsec provides encryption and security. The combination of L2TP and IPsec makes for a high level of security, but puts a strain on connection, resulting in slower latency.
Today, the combination of L2TP and IPsec is used by several VPN providers like Ivacy to provide better VPN support for older systems.
PPTP
Talking about the oldest VPN protocols, the Point-to-Point Tunneling Protocol (PPTP) was also launched in the 1990s and played an important part in developing VPN technology as a whole. PPTP is known for offering great speeds and incredible usability.
At the same time, PPTP's encryption policies like Microsoft Point-to-Point Encryption (MPPE) remain outdated and at risk of modern attacks. While it's not used as a go-to protocol for VPN services, some providers include PPTP for legacy devices or low-security tasks like accessing geo-restricted content.
SSTP
Secure Socket Tunneling Protocol (SSTP) was introduced by Microsoft in 2006. SSTP was primarily developed for Windows platforms to provide safe VPN connections. This protocol uses Secure Sockets Layer (SSL) and Transport Layer Security (TLS) encryption to secure connections and bypass restrictive firewalls.
SSTP works seamlessly with all Windows devices, offering great performance for Microsoft users. PureVPN and StrongVPN offer SSTP as an option with their other services for those who need a secure and firewall-friendly protocol.
How to Choose the Right VPN Protocol for Different Scenarios
If you're looking for the best VPN protocol to support your online activities, you first have to define the exact activities you need a VPN for. It could be bypassing geo-restricted content like watching your favorite shows on Netflix or protecting your work online by adding another layer of security.
Best Protocol for Streaming
Streaming has become extremely popular ever since the first YouTubers started sharing moments from their sessions. Since then, this activity has taken off, so if you're someone who's interested in taking your streaming to the next level, WireGuard is probably the best VPN protocol for you.
It's the fastest VPN protocol there is today, offering smooth video playback, minimal buffering, and the ability to stream comfortably in 4K. Plus, WireGuard's advanced encryption algorithms secure your streaming activities without compromising on connection speeds.
Best Protocol for Torrenting
Despite being a hot topic throughout the years, torrenting remains a popular tool for downloading content online. While torrenting in itself isn't illegal, it all depends on the kind of content you're downloading.
If you're looking to download content that doesn't contradict any copyright laws, you could look into VPN service providers that utilize OpenVPN. Since torrenting requires high-speed connections to download or share files, OpenVPN can keep your online connectivity safe and protected.
Additionally, OpenVPN can be configured however you like, so if you need more performance, you can adjust the settings to suit your needs.
Best Protocol for Gaming
Much like with streaming, gaming is an internet-intensive activity. That's why WireGuard is also the best choice here thanks to its high speed and low latency. Naturally, the quality of your gaming experience depends on more than just a stable internet connection, you have to consider the equipment requirements for every game, and your individual setup.
Still, a stable internet connection remains a key component. WireGuard's lightweight codebase and fast encryption algorithms will allow you to enjoy your favorite games without worrying about interruptions or lags.
Best Protocol for General Browsing
If you're someone who's looking for a quick and easy way to secure your basic online activities and needs, IKEv2/IPsec is a great choice. This protocol strikes the perfect balance between security and performance, offering reliable connection speeds and protected data transmission.
Maintaining a stable connection is something the IKEv2 and IPsec protocol excels in, so for general browsing and day-to-day tasks, this protocol would be the right choice for you. As a bonus, since this protocol is one of the most popular ones on the market, you can be sure that most of the major VPN service providers will offer this protocol.
Best Protocol for Mobile Users
Most VPN providers make sure to tailor their services for multiple device use, no matter the operating system. However, for mobile users, the best option would be the IKEv2 and IPsec protocol.
Its technology allows for smooth and interruption-free reconnection and switching between networks, including going from Wi-Fi connection to mobile data. As a bonus, convenient switching isn't the only benefit, you can be sure that all your data will be completely secured with the IKEv2 and IPsec protocol.
VPN Protocols and Security
VPN protocols are designed to provide secure connections over the internet, but as we already laid out, not all protocols offer the same level of protection. Before you choose a VPN service with a specific protocol, it's important to understand the main security aspects.
Common Vulnerabilities in VPN Protocols
- Weak encryption: some VPN protocols like the older PPTP use outdated encryption policies (notably the MPPE) that result in vulnerabilities that attackers can take advantage of.
- Lack of authentication methods: even the VPN protocols with the most high-security policies can be at risk of malicious individuals and systems if the proper authentication methods aren't set up.
- Protocol leaks: security threats are a real problem, but often it's not due to the code or lax security measures, but poor configuration. For example, an improperly configured L2TP/IPsec or PPTP protocol could result in traffic leaks to unprotected servers.
- Man-in-the-Middle (MITM) attacks: VPN protocols that don't use secure key exchange or verification processes can be at risk from attackers attempting to intercept and manipulate data during transmission.
- Incorrect implementation: as with poor configuration, incorrect implementation is just as big of a problem even for the most secure VPN protocol like OpenVPN or WireGuard.
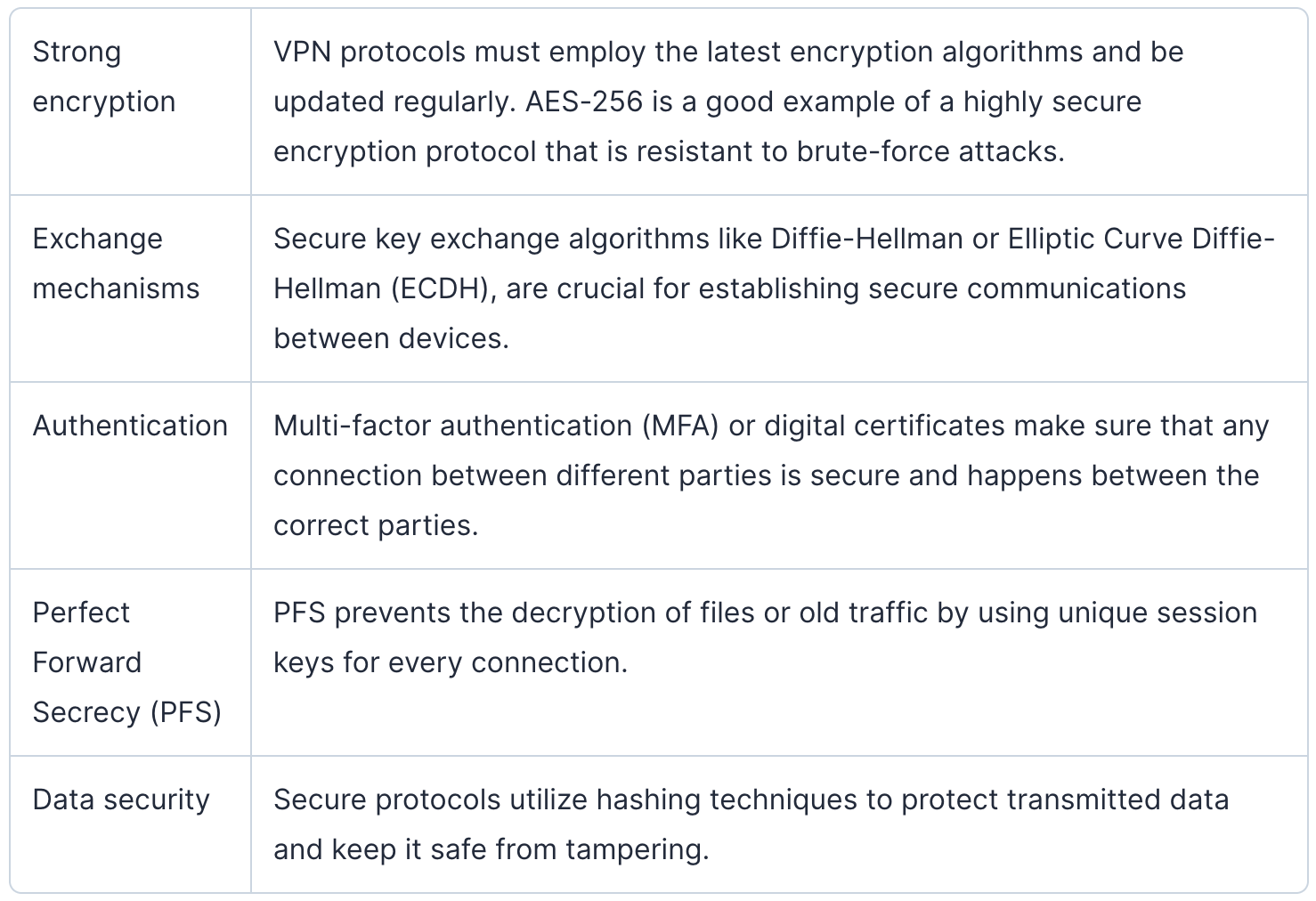
What Makes a Protocol Secure?
A truly secure VPN protocol relies heavily on data integrity, privacy, and resistance to attack. To define each of the key aspects that help make a protocol secure, here's a more detailed table:
Real-world Examples of Breaches (and How Protocols Respond)
No matter what encryption algorithms and other security measures a VPN uses, attacks and breaches happen. This could be due to protocol weakness, misconfiguration, and other factors. Let's look at some of the most notable breach events.
OpenVPN and Heartbleed
In 2014, the infamous Heartbleed bug was discovered in the OpenSSL library, used by OpenVPN and other secure services. The bug is known for allowing attackers to exploit vulnerabilities in the SSL/TLS protocol to read sensitive data like passwords, encryption keys, and session tokens from servers.
The OpenVPN community quickly responded to this issue once it was discovered and patched up the Heartbleed vulnerability. All users were also immediately notified to update the software as soon as possible. This event just goes to show how important regular updates and maintenance are.
WireGuard and Potential Weaknesses
WireGuard is regarded as the most modern and secure protocol today. However, the new technology behind WireGuard has raised concerns about potential vulnerabilities in its initial design. To back this up, in early audits researchers noted some limitations in the protocol's key management and handling of handshakes.
WireGuard may not be open source, but its development team is continuously working to improve the new protocol to address any security and encryption issues found during audits. Plus, to maintain WireGuard's good name and position as the fastest protocol, the team regularly updates the software, allowing VPN providers to use this protocol with confidence.
Conclusion
It used to be that only licensed specialists could help consult on tech questions like what software or hardware to use. Today, with so many choices for an average user, we can select the best options ourselves. This is especially true with VPN services.
Whether you're just starting or have some experience with VPN providers, CometVPN caters to a wide variety of people. We provide lightning-fast and industry-level security for all your needs, be it gaming, streaming, accessing content, or performing work tasks online.
To ensure the best performance, online safety, and speed, CometVPN utilizes top-tier protocols like OpenVPN and WireGuard, allowing for a smooth transition between these protocols for the best user experience. If you're curious, why not try CometVPN with a 30-day guarantee? Get started right away!

Author
Adomas Šulcas
Chief Operating Officer at Growth Bite
Adomas is a technical writing expert who founded Growth Bite, a digital marketing company, focused on providing high-value SEO and content marketing services to SaaS companies.
Related articles
4 min read
Ethernet vs Wi-Fi: Which One is Better?
Ethernet and Wi-Fi are the two main ways to connect your computer to the internet. While Wi-Fi has received significantly more attention in recent years, especially among consumers, due to its simplicity and flexibility, ethernet is still widely used in various other applications.
Even if Wi-Fi is significantly more popular, it isn’t strictly better. Both methods have their benefits and drawbacks. Wi-Fi’s popularity comes from its ease-of-use and flexibility, but an ethernet connection can be much more useful in certain scenarios.

Adomas Šulcas
5 min read
How to Change Chrome Proxy Settings: The Ultimate Guide
A proxy server is an easy alternative to a VPN that can perform most of the functions of the latter. It’s a server that stands between your device and the destination server, taking your connection requests and forwarding them in your name.
Destination servers in almost all cases see the proxy server as the originator of the request. As such, proxies are widely used in various, mostly business-related applications whenever privacy, security, location changing, and several other factors are at play.

Guoda Šulcaitė